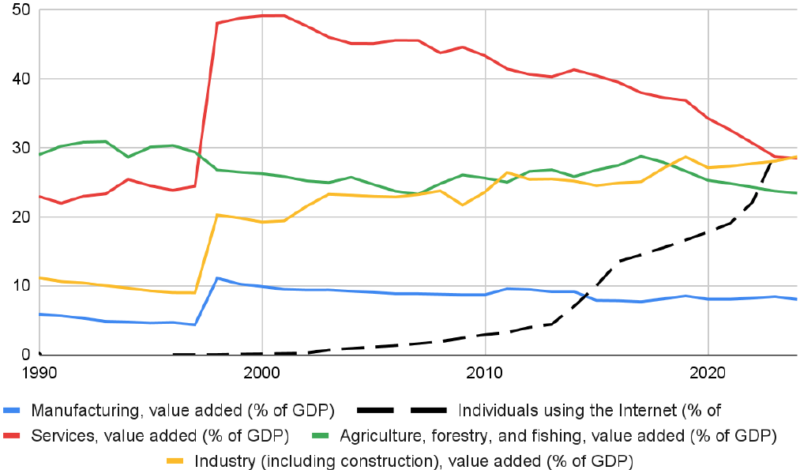
Tanzania Is Getting Online. Its Digital Economy Isn’t Following.
Across most of the developing world, the story of the last two decades has been a hopeful one: as people come online, the digital economy grows, services expand, new businesses take root, people make more money and lift themselves by…
Anthropic Tries to Revive the “AI Pause”
Back in 2023, the Future of Life Institute issued a open letter calling to “pause giant AI experiments” before runaway AI destroyed humanity. Three years later, machine learning applications have expanded in use and capability, yet humans are still…
Running a Race Looking Backwards: US Digital Export Controls
Congress has introduced another law tightening export controls on additional segments of the semiconductor industry (the MATCH Act). Like all the others, it is based on the premise that US technological leadership and national security is advanced by looking backwards…
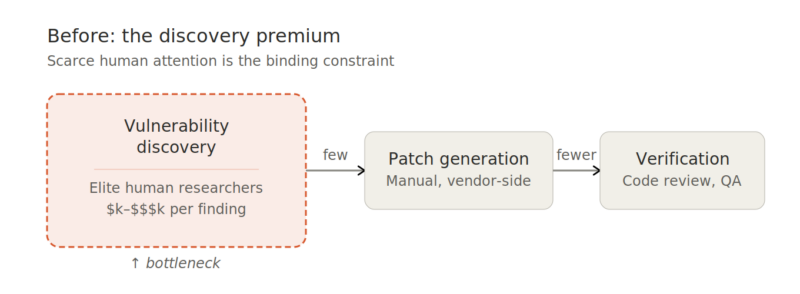
AI, Project Glasswing, and the Changing Institutional Economics of Bugs
On April 7, Anthropic published a 244-page system card for a model that will not be made generally available for now. Claude Mythos Preview, the company’s newest frontier model, is “capable of identifying and then exploiting zero-day vulnerabilities in every…
India’s crude Internet censorship regime
Sections 69A and 79 of the Information Technology Act, 2000, empower the indian government to issue blocking orders to ISPs and intermediaries. The licensing agreement for ISPs explicitly requires that they “block Internet sites […] as identified and directed by…
Fake Cybersecurity: The FCC Router Ban
On March 23, 2026, the Federal Communications Commission (FCC) issued a Memorandum and Order banning the import of “covered” consumer-grade networking hardware. The decision demonstrates once again how the Trump administration’s economic nationalism and its use of “national security” claims…
What Everyone Is Missing About Anthropic and the Pentagon
On February 27th, President Trump directed all federal agencies to cease using Anthropic’s technology after the company refused the Pentagon’s demand to allow lawful use of its AI models for mass domestic surveillance and fully autonomous weapons. Much of the…
Beyond Borders: How Threat Intelligence Provenance Can Save Global Cybersecurity From Geopolitical Fragmentation
In mid-January 2026, the Chinese government allegedly announced a sweeping ban on cybersecurity software from more than a dozen U.S. and Israeli firms, including industry giants like Palo Alto Networks, CrowdStrike, and Check Point. The stated reason: concerns that foreign…
Did an AI application really “bully” a human?
There is a battle over the reputation of advanced AI applications going on in the news. Two worldviews conflict: Are we unleashing dangerous forces that threaten humanity? Or are we just making computers and software do a lot of new…
Digital Media and the American Civil Conflict
Operation “Metro Surge” in Minneapolis-St. Paul, USA, has now attracted national and worldwide attention. Both sides in this conflict see it as a showdown. It is a showdown, and it matters who wins. In this blog, we try to focus on…